Incident Response & Mitigation
Incident Response and Mitigation Services offer rapid containment, investigation, and recovery from cyber incidents, minimizing impact and ensuring your organization’s resilience against future threats.
A comprehensive approach to handling cyber incidents, including swift detection, containment, and neutralization of threats. Our process ensures minimal disruption, rapid recovery, and protection of critical assets. We also provide detailed post-incident analysis and recommendations to strengthen your defences against future attacks.
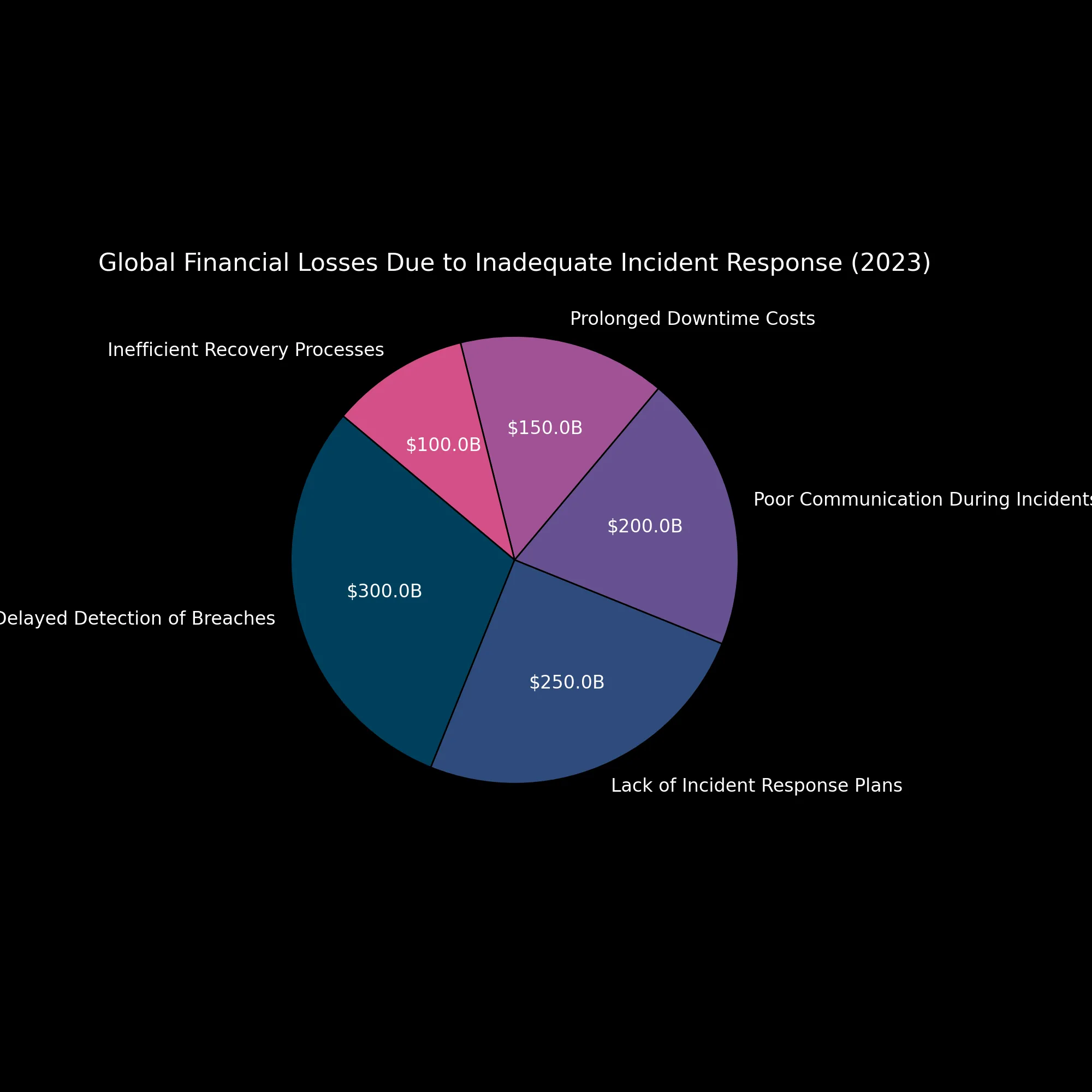
Global Financial Fallout from Inadequate Incident Response
In today’s hyper-connected world, incident response isn’t optional—it’s survival. When a breach occurs, the difference between swift containment and chaotic delay can cost billions.
At a global scale, the numbers are staggering:
- 🌐 Total global cybercrime losses (2023): £720 billion (avg)
- ❌ Attributed to poor incident response: £200 billion
- ✅ Losses preventable with mature IR practices: £130 billion
Without a tested and tactical response capability, organisations fall victim not just to the initial breach—but to compounding financial damage, reputation collapse, and regulatory punishment.
QuantumSabre’s military-grade Incident Response services are engineered to eliminate this margin of loss — restoring operational integrity, shielding reputation, and hardening systems against future compromise.
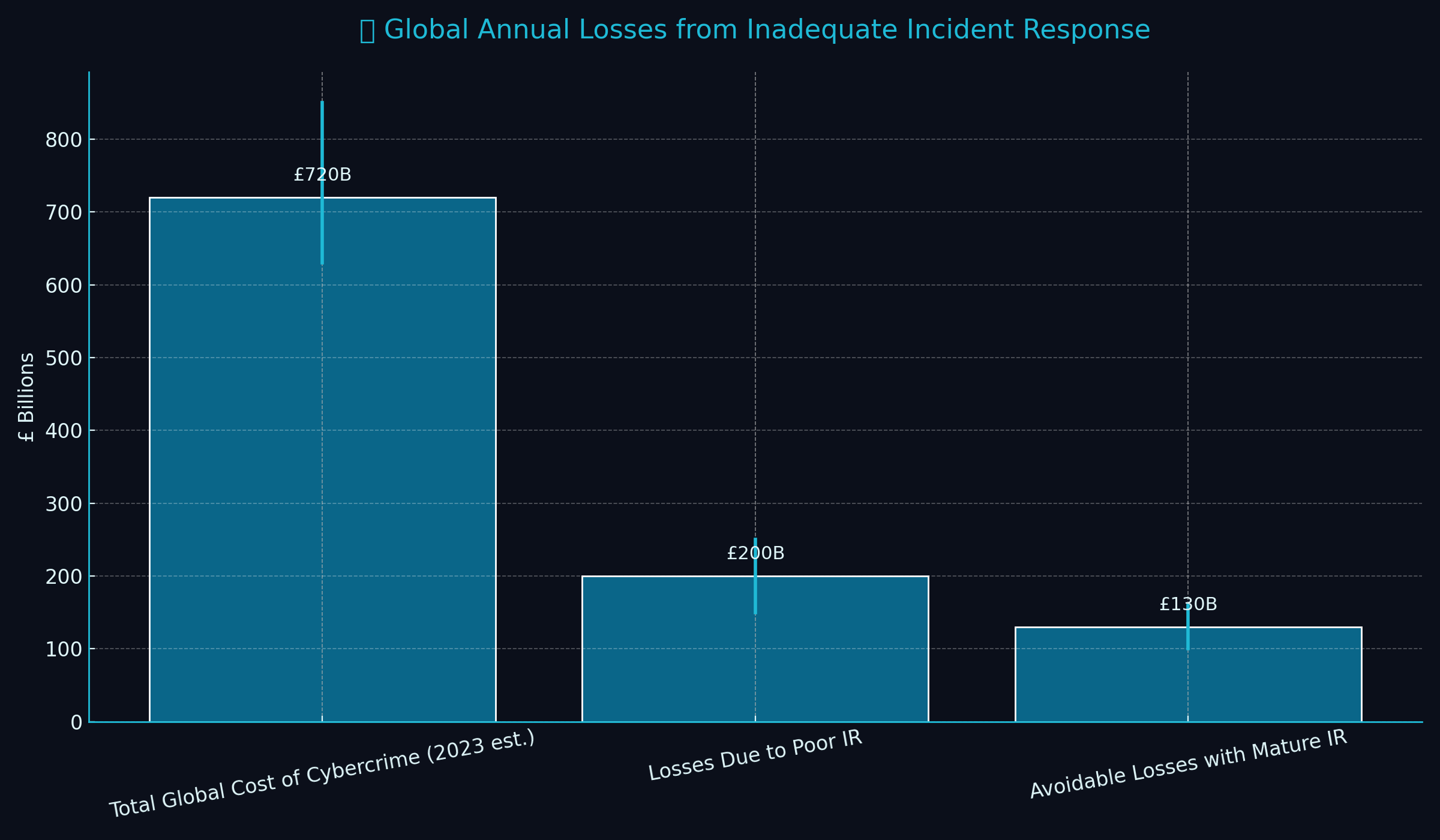
📚 Sources: IBM Security “Cost of a Data Breach Report 2023” · Statista · Ponemon Institute Global IR Benchmarking Reports
QuantumSabre Incident Response and Mitigation Methodology and Assurance
At QuantumSabre, we understand the critical importance of rapid, effective Incident Response and Mitigation Services. Our approach is designed to minimize impact, restore operations swiftly, and prevent future incidents. Here’s how we deliver:
Methodology
1. Preparation
- Proactive Readiness: We establish tailored incident response plans, develop communication protocols, and train your team to respond effectively.
- Threat Intelligence Integration: Incorporating real-time threat intelligence to anticipate and prepare for emerging risks.
2. Identification
- Continuous Monitoring: Advanced monitoring tools detect anomalies and potential breaches in real-time.
- Forensic Analysis: Detailed examination of alerts to determine the scope and severity of the incident.
3. Containment
- Immediate Action: Isolating affected systems to prevent further spread of threats.
- Tactical Measures: Implementing temporary solutions to maintain business continuity while addressing vulnerabilities.
4. Eradication
- Root Cause Analysis: Identifying and eliminating the source of the breach, such as malware or compromised accounts.
- System Cleansing: Removing malicious files, patching vulnerabilities, and securing configurations.
5. Recovery
- System Restoration: Safely restoring operations from clean backups and verifying integrity.
- Validation: Conducting thorough tests to ensure the environment is secure and fully operational.
6. Lessons Learned
- Post-Incident Review: Analyzing the incident to identify areas for improvement.
- Actionable Insights: Updating policies, procedures, and infrastructure based on findings.
Assurance
- Proactive Prevention: Leveraging threat intelligence and advanced tools to reduce the likelihood of incidents.
- 24/7 Availability: Our team is ready to respond anytime, ensuring rapid containment and recovery.
- Tailored Solutions: Customized plans and actions based on your unique environment and needs.
- Compliance and Standards: Aligning with global frameworks like NIST, ISO 27001, and GDPR to ensure legal and regulatory compliance.
- Ongoing Support: Post-incident consulting to enhance your cybersecurity posture and resilience against future threats.
With Quantumsabre’s Incident Response and Mitigation Services expertise, your organization is assured of swift, efficient handling of cyber incidents, minimizing downtime and protecting critical assets.
Why EDR Alone Is No Longer Enough: A 2025 Reality Check
In 2025, many businesses still trust Endpoint Detection and Response (EDR) as their primary cybersecurity defense.While EDR remains an important…
The Truth About Cybersecurity Firms
🔐 The uncomfortable truth in cybersecurity: Most vendors inspect your traffic and call it “monitoring.” At QuantumSabre, we don’t inspect…
Trade Wars, Recession & Cyber Risk: Why SMBs Are Now the Frontline Target
Cybercrime Thrives in Chaos In times of economic strain, the predators come out to play. As the 2025 trade war…
