SECURITY ARCHITECTURE DESIGN
Precision-Engineered Cyber Defense. Built for Survivability. Hardened to Protect What Matters.
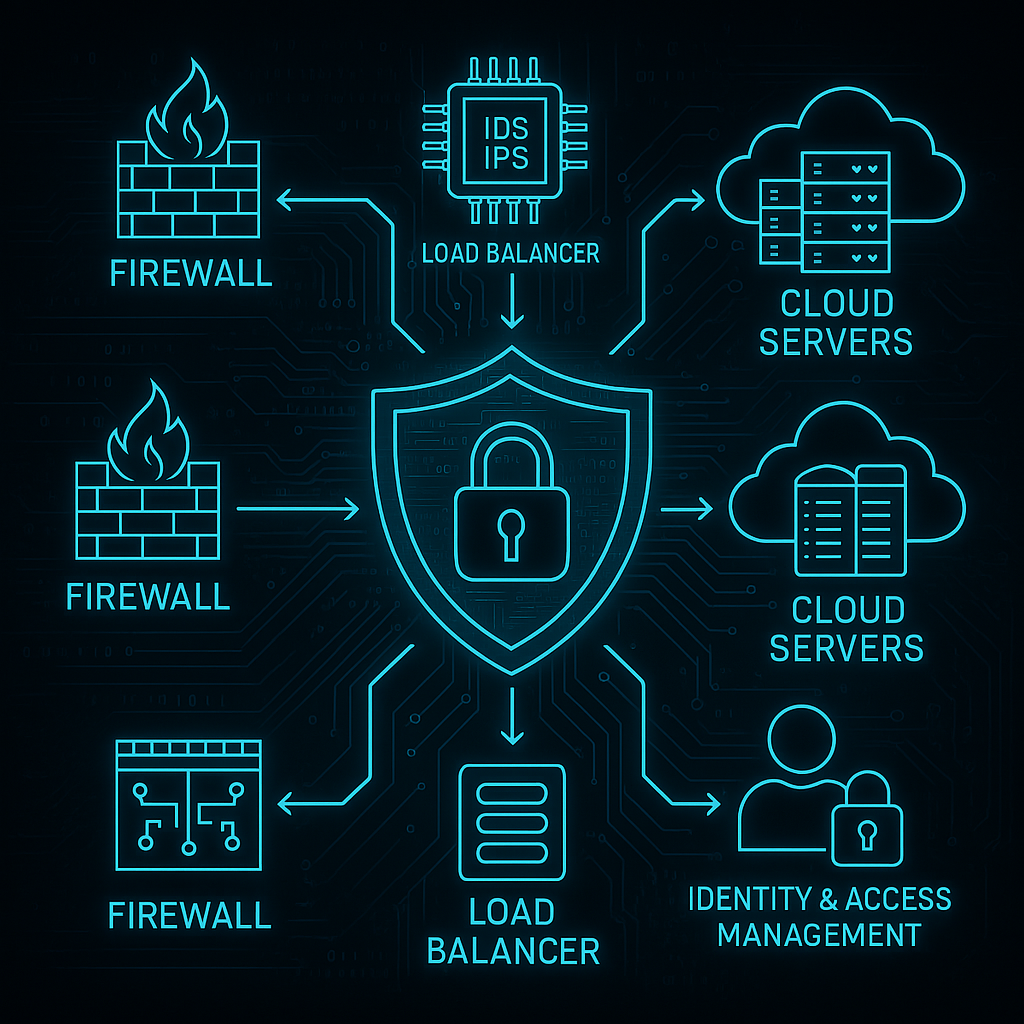
QuantumSabre’s Security Architecture Design delivers precision-built, military-grade defense frameworks engineered to withstand modern threats.
Our architectures are resilient, scalable, and tailored to your exact infrastructure — no bloat, no assumptions.
We proactively identify vulnerabilities, embed hardened controls, and enforce zero-trust principles across every layer.
Every solution is built to ensure full compliance, operational integrity, and long-term survivability — even under advanced persistent threat conditions.
Cost of Essential Security Architecture Package
Service Description:
- Foundational security design focusing on core organizational needs.
Scope:
- Identification of business requirements and risk assessment.
- Definition of security principles and policies.
- Data protection strategies and access control mechanisms.
- Network segmentation and perimeter security design.
Pricing:
- Daily Rate: £750 – £1,250 per day.
- Estimated Duration: 10 – 15 days.
Note: Pricing and scope are indicative and may vary based on specific organizational requirements and complexities. For a customized quote, please contact our sales team.
These service bundles are designed to provide flexible and comprehensive support to organizations seeking to enhance their cybersecurity posture.
Cost of Advanced Security Architecture Package
Service Description:
- Comprehensive security design encompassing advanced organizational requirements.
Scope:
- Includes all elements of the Essential Package.
- Application security and secure development practices.
- Identity and Access Management (IAM) framework design.
- Endpoint and device security measures.
- Data encryption strategies and integrity assurance.
Pricing:
- Daily Rate: £800 – £1,400 per day.
- Estimated Duration: 20 – 25 days.
Note: Pricing and scope are indicative and may vary based on specific organizational requirements and complexities. For a customized quote, please contact our sales team.
These service bundles are designed to provide flexible and comprehensive support to organizations seeking to enhance their cybersecurity posture.
Cost of Enterprise Security Architecture Package
Service Description:
- Holistic security architecture design tailored for large-scale enterprises with complex infrastructures.
Scope:
- Includes all elements of the Advanced Package.
- Logging, monitoring, and incident response planning.
- Compliance and regulatory requirements alignment.
- Security awareness and training programs.
- Regular security audits and updates framework.
Prices:
- Daily Rate: £900 – £1,600 per day.
- Estimated Duration: 30 – 40 days.
Note: Pricing and scope are indicative and may vary based on specific organizational requirements and complexities. For a customized quote, please contact our sales team.
These service bundles are designed to provide flexible and comprehensive support to organizations seeking to enhance their cybersecurity posture.
Accurately quantifying the financial impact of inadequate security architecture design in the UK is challenging due to the complex and varied nature of cyber incidents. However, the “Cyber Security Breaches Survey 2023” by the UK government provides some insights:
- Prevalence of Cyber Attacks: Approximately 32% of UK businesses identified a cyber attack in the past 12 months. GOV.UK
- Financial Impact: Among medium and large businesses that experienced breaches, exceed £100,000 to £500,000 for SMBs..
While these figures offer a glimpse into the financial repercussions of cyber incidents, they don’t isolate the specific costs attributable solely to deficiencies in security architecture design. The total economic impact encompasses various factors, including operational disruptions, reputational damage, regulatory fines, and recovery expenses.
For a more comprehensive understanding, consulting detailed industry reports or engaging with cybersecurity experts would be advisable.
Why EDR Alone Is No Longer Enough: A 2025 Reality Check
In 2025, many businesses still trust Endpoint Detection and Response (EDR) as their primary cybersecurity defense.While EDR remains an important…
The Truth About Cybersecurity Firms
🔐 The uncomfortable truth in cybersecurity: Most vendors inspect your traffic and call it “monitoring.” At QuantumSabre, we don’t inspect…
Trade Wars, Recession & Cyber Risk: Why SMBs Are Now the Frontline Target
Cybercrime Thrives in Chaos In times of economic strain, the predators come out to play. As the 2025 trade war…
